ECU programming and immobilizer pairing are inseparable in many modern vehicles because the engine computer (ECU/ECM) often must “trust” the anti-theft system before it will allow the engine to start. If the ECU software or the immobilizer relationship is wrong, the car can crank but not start, start then stall, or refuse to communicate during service operations.
Next, this guide explains why pairing fails, what warning signs point to an immobilizer mismatch, and how to plan a safe, legitimate workflow that prevents costly mistakes like corrupted software or unnecessary module replacement.
Then, you’ll learn how to choose tools and service paths—dealer-level procedures, aftermarket equipment, or specialized programming services—based on vehicle security design, job scope, and customer constraints.
Introduce a new idea: once you understand how the ECU/ECM, key transponder, and immobilizer controller share security data, you can diagnose problems faster and decide whether you need programming, pairing, repair, or a broader electrical fix.
What is ECU programming and immobilizer pairing, and why are they linked?
ECU programming and immobilizer pairing is the process of updating or configuring an engine computer (ECU/ECM) and synchronizing it with the vehicle’s anti-theft authorization system so the engine will only run when valid credentials are present.
To better understand why this linkage matters, think of the ECU as the “decision-maker” and the immobilizer as the “gatekeeper”: both must agree before fuel, spark, and starting authorization are granted.
What does “ECU programming” include?
ECU programming typically includes software flashing (writing firmware/calibration), coding (configuring options), and adaptation resets that align the ECU with the vehicle’s hardware. In a repair context, ECU programming may be required when:
- An ECU is replaced (new or used) and must be configured to the car
- A software update resolves drivability, emissions, or communication issues
- A repair requires re-initialization of learned values (throttle, idle, misfire counters, etc.)
- A vehicle has security-linked modules that must be “introduced” to each other
The key point is that programming is not just “tuning.” In many OEM workflows, it is a controlled process that writes data, verifies integrity, and confirms configuration consistency across multiple modules.
What does “immobilizer pairing” actually do?
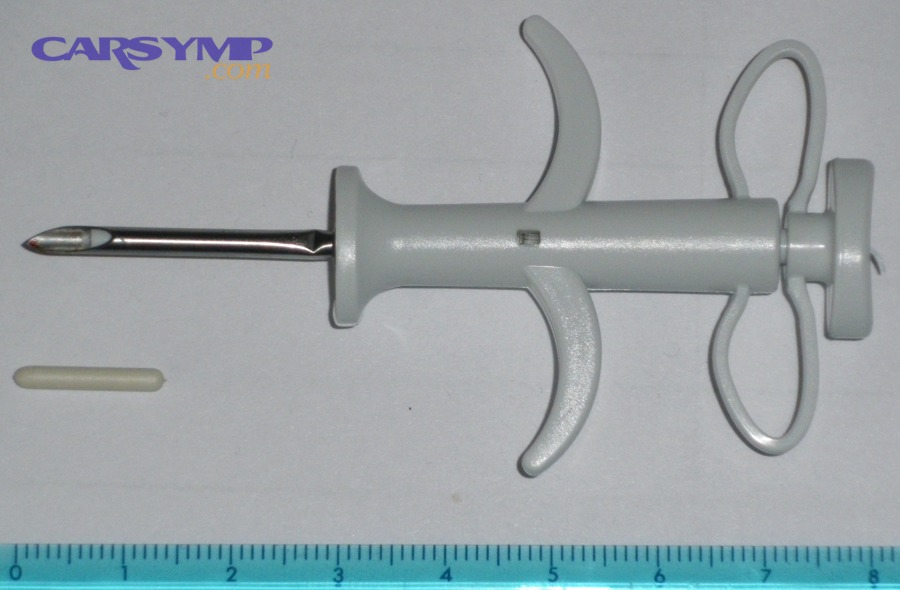
Immobilizer pairing aligns security credentials across components—commonly the key transponder, immobilizer controller (sometimes integrated into the instrument cluster, BCM, or a dedicated immobilizer module), and the ECU/ECM. When pairing is correct, the vehicle can validate that:
- The key is legitimate (transponder ID and crypto response)
- The immobilizer controller approves start authorization
- The ECU recognizes the authorization and enables engine operation
A practical way to explain it to customers is: the immobilizer is a security handshake—if the handshake fails, the ECU can behave like it’s “locked,” even if the engine hardware is fine.
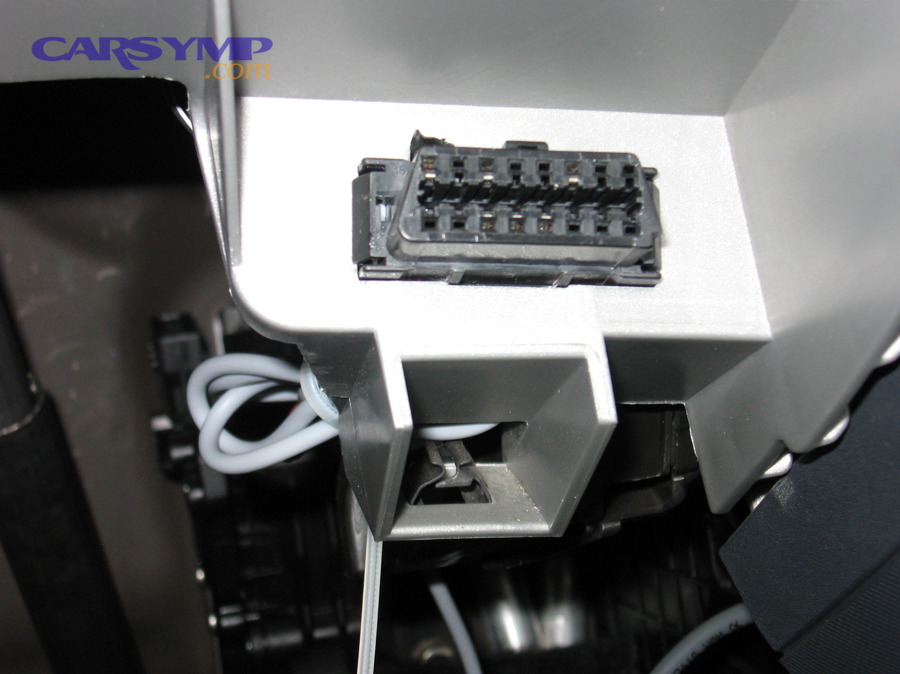
Which components are involved (ECU, BCM, key transponder, cluster)?
Most systems involve a chain of trust. The exact architecture varies, but these are common participants:
- Key/FOB transponder: the credential presented to the vehicle
- Immobilizer controller: validates the key and grants authorization
- ECU/ECM: enforces authorization by enabling fuel/spark/start
- BCM (Body Control Module): often manages key learning and security access
- Instrument cluster: in many platforms, security logic is partially or fully integrated here
Because these components share security data, replacing just one can break the chain—especially with used modules or mismatched software versions.
Do you always need immobilizer pairing after ECU programming?
No—you do not always need immobilizer pairing after ECU programming because not every ECU software update changes security data, not every vehicle ties immobilizer authorization to the ECU, and some platforms handle pairing automatically when OEM procedures are followed.
However, pairing becomes necessary when the update or module change affects identity, security credentials, or configuration dependencies across the anti-theft network.

When pairing is required (replacement ECU, virgin ECU, security reset)
Pairing is commonly required when:
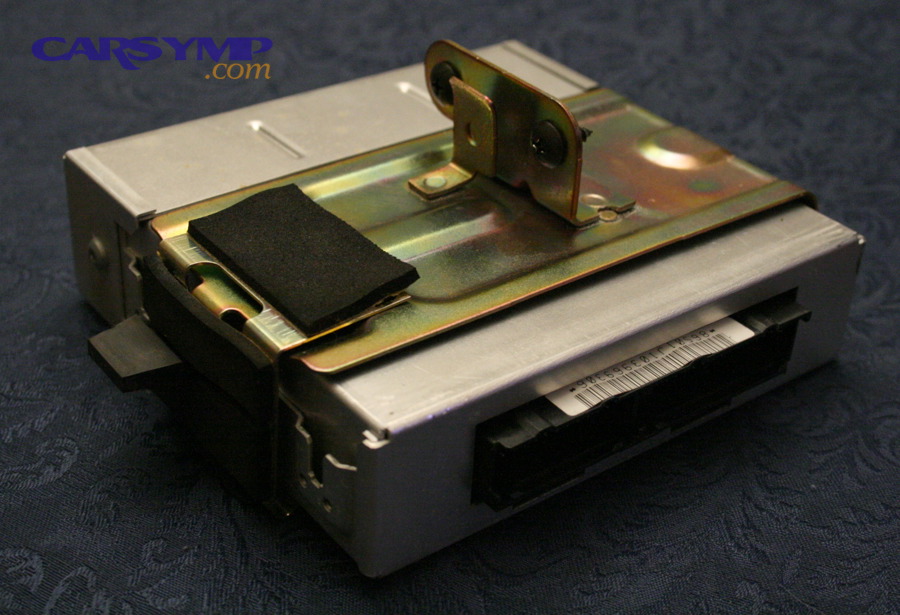
- ECU/ECM replacement: new or used ECU must be introduced to the immobilizer
- “Virgin” or uninitialized ECU: must be personalized to the car
- Security reset procedures: some OEM workflows require re-synchronization after resets
- All keys lost scenarios: security systems may require broader credential relearning (handled by authorized service providers)
Because security is involved, most manufacturers gate these functions behind credentialed access, time delays, or server-based authorization.
When pairing is not required (certain updates, non-security ECUs)
Pairing may not be required when:
- The programming is a standard calibration update on the original ECU
- The vehicle’s immobilizer does not authenticate through the ECU (architecture-dependent)
- The OEM process updates multiple modules in a coordinated way and maintains security alignment
In short, the safest assumption is: if you changed the ECU identity or replaced the ECU, pairing is likely required; if you only updated software on the original ECU, pairing may not be required—but you must confirm per platform.
How to check if pairing is needed before touching anything
Before initiating any service operation, confirm:
- Whether the ECU is original or replaced (part number and identifiers)
- Whether the immobilizer and ECU show “matched/authorized” status in scan data
- Whether the OEM procedure explicitly calls out pairing, personalization, or immobilizer registration
- Whether the vehicle has a security warning lamp or anti-theft messages after the change
This pre-check prevents a common trap: doing a full reflash when the real issue is a security mismatch—or vice versa.
What symptoms indicate an ECU/immobilizer mismatch?
The most common symptoms of an ECU/immobilizer mismatch are crank-no-start, start-then-stall, and security/immobilizer warnings, often combined with scan-tool data showing “start authorization: NO” or similar status.
Next, it’s important to separate immobilizer mismatch symptoms from mechanical failures, because both can look identical from the driver’s seat.
Crank-no-start vs start-then-stall patterns
Immobilizer-related patterns often look like this:
- Crank-no-start: starter operates normally, but engine never fires
- Start then stall in 1–2 seconds: engine catches briefly, then fuel/spark is cut
- Intermittent start authorization: starts sometimes with certain keys or environmental conditions
A mismatch can be consistent or intermittent depending on whether the system is failing hard (wrong ECU/security data) or soft (weak key signal, antenna issue, network fault).
Security light behavior and scan data (authorization status)
Security indicator behavior varies, but typical signals include:
- Immobilizer light flashing rapidly during crank
- Security message on cluster (“Key not recognized,” “Immobilizer active,” etc.)
- Scan data showing immobilizer active or start allowed = NO
This is where ECU diagnosis saves time: rather than guessing, you use scan data, module status, and network health to identify what the car believes is wrong.
Misdiagnosis traps: ECU vs sensor/wiring fault diagnosis
A major pitfall is confusing an immobilizer lockout with a hardware fault. ECU vs sensor/wiring fault diagnosis should follow logic:
- If authorization is NO, do not chase fuel pressure first
- If authorization is YES but it still won’t start, move to ignition/fuel/air diagnostics
- If the ECU won’t communicate reliably, investigate power/ground/network before declaring the ECU “dead”
This approach reduces unnecessary parts replacement and prevents “stacking” problems—like installing a used ECU when the true issue was a wiring fault at the immobilizer antenna.
Which tools and prerequisites are necessary for safe ECU programming and pairing?
You need the right tools and prerequisites for safe ECU programming and pairing: stable power, proper diagnostic communication, and authorized security access, plus documentation that matches the exact vehicle configuration.
Then, once the basics are in place, you can choose the least risky route—OEM, aftermarket, or specialty service—based on what the vehicle allows.
Battery support, voltage stability, and why reflashes fail
Programming is sensitive to voltage and communication integrity. Risk rises when:
- Battery voltage drops under load (cooling fans, pumps, modules waking up)
- A charger “pulses” unstable voltage during flash writes
- Communication is interrupted by sleep cycles or bus errors
From a risk management standpoint, “stable power” is not a nice-to-have—it is the difference between a clean update and a corrupted ECU that requires recovery.
OEM vs aftermarket scan tools: what matters for immobilizer functions
For immobilizer work, what matters most is not the brand name—it’s capability:
- Can the tool access immobilizer/BCM security functions for that platform?
- Can it perform guided procedures with proper prompts and confirmations?
- Does it support credentialed access where required?
- Can it generate a scan report showing authorization status and faults?
In many cases, immobilizer functions are restricted, so even a strong aftermarket tool may still be limited without OEM pathways.
Access requirements: security credentials, PIN/seed-key, and legal authorization
Because immobilizer systems are anti-theft by design, many manufacturers require:
- Proof of ownership or service authorization
- Credentialed accounts (dealer/authorized providers)
- Online security access or time delays
- Logging and audit trails
For legitimate shops, the operational takeaway is simple: plan your workflow assuming security access may be required, and avoid promising same-day results until you verify what the platform allows.
How do you perform ECU programming and immobilizer pairing in a legitimate workflow?
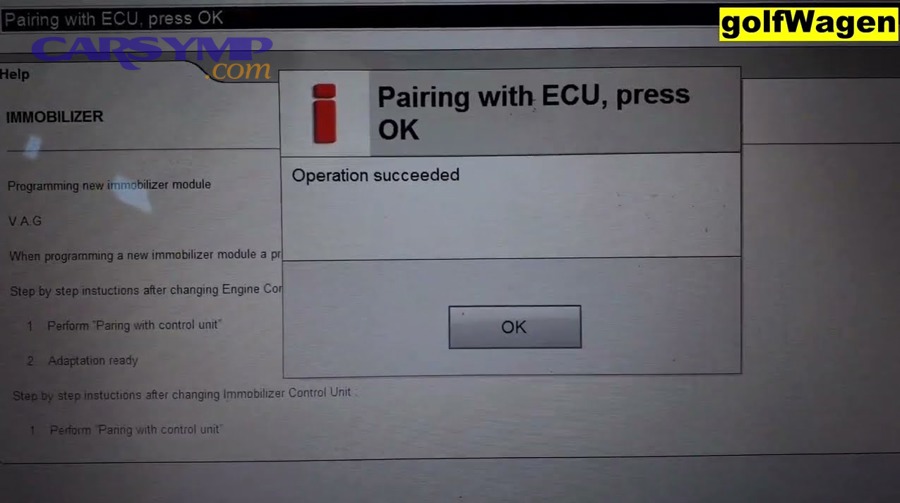
A legitimate workflow for ECU programming and immobilizer pairing is a 7-step process: verify authorization, confirm system status, stabilize power, follow OEM procedure, validate communication, confirm start authorization, and document results—so the vehicle starts reliably and security remains intact.

Below, the workflow stays intentionally platform-neutral and safety-focused, because exact immobilizer procedures vary by manufacturer and are often restricted to authorized methods.
Step-by-step workflow (planning, backup, programming, pairing, validation)
- Verify ownership/service authorization
- Confirm customer identity and vehicle documentation
- Record VIN, module part numbers, and current symptoms
- Baseline scan and network health check
- Save a full scan report (all modules)
- Confirm ECU/BCM/immobilizer communication status
- Stabilize power and isolate risk factors
- Use appropriate battery support
- Disable nonessential loads where safe/allowed (lights, HVAC)
- Confirm ECU identity and compatibility
- Verify ECU/ECM part number and software family
- Confirm it is correct for engine, transmission, emissions, and region
- Perform ECU programming using approved procedure
- Follow OEM service information for sequencing
- Avoid interruptions; do not cycle ignition unless prompted
- Perform immobilizer pairing/personalization (if required)
- Execute the authorized immobilizer function for the platform
- Confirm “start authorization” status changes from NO to YES
- Validation drive cycle and documentation
- Verify starts, no security warnings, and stable idle
- Provide the customer with results and recommendations
Post-programming checks: DTCs, readiness, and start authorization
After successful service, validate:
- ECU communicates consistently (no intermittent dropout)
- Immobilizer status is “authorized”
- DTCs are addressed in priority order (security/network before sensor noise)
- Readiness monitors and driveability are appropriate for the job scope
This is where many comebacks are prevented: a car may start in the bay but fail later if the root cause was weak power, poor grounds, or a marginal network connection.
Documentation and scan reports to reduce comebacks
Documenting the process protects both shop and customer:
- Pre-scan vs post-scan reports
- Module IDs and software versions
- Start authorization status confirmation
- Notes on any limitations (e.g., keys not present, follow-up required)
This reinforces professionalism and reduces disputes when a vehicle has multiple overlapping issues.
Which method is best: dealer programming vs aftermarket tools vs bench services?
Dealer programming wins in coverage and security compliance, aftermarket tools are best for cost and broad diagnostics, and bench services can be optimal for special cases like ECU recovery—but the “best” choice depends on security restrictions, vehicle downtime tolerance, and the risk profile of the job.
However, you should decide using objective criteria instead of habit, because immobilizer jobs can become expensive quickly if the wrong path is chosen.
Comparison by cost, time, risk, and coverage
The table below compares common pathways so you can match the method to the job requirement rather than forcing the job into your preferred toolset.
| Method | Best for | Typical strengths | Typical risks/limits |
|---|---|---|---|
| Dealer/OEM programming | Security-linked pairing and latest updates | Highest procedure accuracy; best access | Cost, scheduling delays |
| Aftermarket diagnostic tools | Broad scanning + some service functions | Fast triage; good data viewing | Pairing may be limited by platform security |
| Bench/recovery services | Bricked modules, cloning, specialized repair | Hardware-level recovery options | Vehicle off-road time; needs strict chain-of-custody |
When to use ECU repair vs replacement options
ECU repair vs replacement options depends on failure mode:
- If the ECU has software corruption from an interrupted flash, repair/recovery may be possible
- If the ECU has power supply damage or water intrusion, repair may be viable but must be validated under load
- If the ECU has internal hardware failure affecting communication, replacement may be more predictable
A practical rule: if the ECU’s identity and security relationship can be restored reliably, repair can be cost-effective; if stability is uncertain, replacement (with proper programming/pairing) reduces risk of repeat failure.
When to consider a used ECU risks
When to consider a used ECU risks, evaluate these factors before you install it:
- Security lock-in: many ECUs are “married” to the original immobilizer
- Software mismatch: emissions/region/version differences can create hidden problems
- Unknown history: water damage, overheating, prior tuning, or partial corruption
- Warranty reality: salvage parts often have limited support
Used ECUs can work in the right context, but they demand careful verification and a plan for pairing/personalization—otherwise, they can create a no-start that looks like a new failure.
Evidence: According to a study by Tilburg University from the Economics department area, in 2013, researchers reported that uniform application of electronic engine immobilizers reduced the probability of car theft by an estimated 50% on average in the Netherlands during 1995–2008, highlighting how tightly modern powertrain control and security systems are designed to stay linked. (research.tilburguniversity.edu)
What should you do if pairing fails or the ECU seems “locked”?
If pairing fails or the ECU appears “locked,” you should stop repeated attempts, confirm power/network stability, re-check authorization requirements, and then decide whether you need a controlled recovery path—because repeated failed attempts can escalate the problem and increase downtime.

Next, focus on what the vehicle is telling you through data and behavior instead of guessing, because “locked” often means “not authorized,” not “physically broken.”
Common root causes: voltage drop, wrong software, communication faults
Pairing failures often come from predictable causes:
- Voltage instability during programming or security functions
- Incorrect ECU variant (wrong part number/software family)
- CAN/LIN communication issues (poor grounds, corrosion, module dropout)
- Security access not granted (missing credentials, time delay not completed, server unreachable)
- Key/antenna problems (weak transponder signal or receiver fault)
This is why ECU diagnosis should always include electrical fundamentals: power, ground, network, and status data.
Recovery paths: reattempt rules, module reset, professional escalation
A safe recovery strategy typically includes:
- Follow OEM guidance on how many attempts are allowed and what resets are required between attempts
- Avoid cycling ignition rapidly unless prompted
- If the ECU becomes non-communicative, prioritize restoring communication before further actions
- Escalate to authorized resources when the platform requires credentialed access or server-side approval
If you suspect a partial flash or corrupted state, treat it as a high-risk condition and switch to controlled recovery rather than trial-and-error.
Confirming it’s not a power/ground issue before blaming the ECU
Before declaring an ECU “bad,” validate:
- Battery and charging health under load
- ECU power feeds and grounds voltage drop under crank
- CAN integrity (termination, bus errors, module wake/sleep behavior)
- Connector condition (water ingress, pin tension, corrosion)
This prevents the most expensive misstep in the field: replacing an ECU when the real fault is a ground splice, a corroded connector, or a network issue—then discovering the replacement now also “won’t pair.”
Evidence: According to a study by the University of Leeds from the School of Law, in 2025, the published research summary reported that vehicle electronic engine immobilizers were associated with a long-term reduction in U.S. vehicle theft of about 80% between 1990 and 2020, reinforcing why immobilizer authorization failures can look like “engine problems” even when hardware is fine. (essl.leeds.ac.uk)
What edge cases change the strategy (hybrid/EV ECUs, mileage/cluster sync, and aftermarket keys)?
Edge cases change the strategy because newer platforms add extra security ties—hybrid/EV powertrain modules, mileage/cluster synchronization, and aftermarket key ecosystems can all add new failure points that look like ECU faults but are actually “system alignment” issues.
Moreover, these micro-cases are where shops win or lose time: you either recognize the pattern early, or you burn hours trying to make a normal workflow fit an abnormal system.
How hybrid/EV architectures affect authorization and programming
Hybrid and EV platforms may spread authorization across multiple modules:
- Powertrain control may involve inverter control, battery management, and gateway modules
- Some functions require coordinated updates across several controllers
- “Ready” state may be inhibited by security status or high-voltage system faults
In these cases, programming and pairing strategy must include a broader module map and more careful validation steps.
Cluster/BCM synchronization issues that look like ECU failure
Some vehicles tie identity data to the cluster or BCM. When these elements are mismatched:
- Security authorization can fail even with a correct ECU
- Warning lights may appear unrelated (multiple modules reporting “implausible data”)
- Replacement of one module triggers cascading “component protection” style behavior
The practical fix is not “replace more parts”—it is verifying which module is the security anchor and using the correct authorized process to synchronize.
Aftermarket key considerations without teaching bypass methods
Aftermarket keys and remotes can be legitimate, but they add variability:
- Incorrect transponder type can cause recognition failures
- Poor-quality shells can affect antenna coupling
- Some platforms are highly sensitive to key ID formatting and quality
For safety and compliance, focus on verified components, documented authorization, and controlled procedures—never shortcuts—so immobilizer pairing supports security rather than undermining it.

